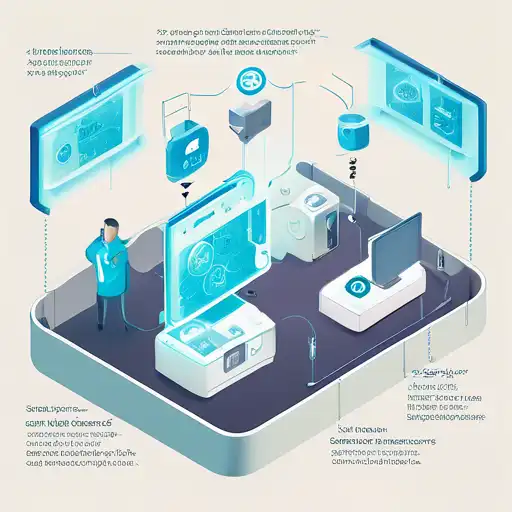
IoT Security Challenges and Solutions
Posted on August 04, 2025 Technology
Understanding IoT Security Challenges. The Internet of Things (IoT) has revolutionized how we interact with technology, embedding connectivity into everyday objects. However, this innovation comes... Read More
Cybersecurity Essentials for Remote Workers
Posted on August 03, 2025 Technology
Introduction to Cybersecurity for Remote Workers. In today's digital age, the shift towards remote work has introduced new cybersecurity challenges. Protecting sensitive data and maintaining... Read More

How to Build a Strong Cybersecurity Strategy
Posted on August 03, 2025 Technology
Understanding the Importance of Cybersecurity. In today's digital age, cybersecurity is not just an option but a necessity for businesses and individuals alike. With the increasing number of cyber... Read More
The Latest Trends in Cybersecurity Defense
Posted on August 03, 2025 Technology
Introduction to Modern Cybersecurity Defense. In the ever-evolving digital landscape, cybersecurity defense mechanisms are constantly being updated to counteract the sophisticated tactics of... Read More
Cloud Security Best Practices for Businesses
Posted on August 03, 2025 Technology
Introduction to Cloud Security. In today's digital age, businesses are increasingly moving their operations to the cloud. While this shift offers numerous benefits, including scalability and cost... Read More

How Blockchain is Enhancing Data Security
Posted on August 03, 2025 Technology
The Revolutionary Impact of Blockchain on Data Security. In the digital age, data security has become a paramount concern for individuals and organizations alike. With the increasing prevalence of... Read More

The Security Challenges of IoT Devices
Posted on July 23, 2025 Technology
Understanding the Security Challenges of IoT Devices. The Internet of Things (IoT) has revolutionized how we interact with technology, embedding smart capabilities into everyday objects. From... Read More
Cybersecurity Trends That Are Shaping the Future
Posted on July 22, 2025 Technology
Introduction to Cybersecurity Evolution. In the digital age, cybersecurity has become a cornerstone of technological advancement and personal privacy. As we navigate through 2023, several emerging... Read More

How to Stay Safe from Phishing Attacks
Posted on July 22, 2025 Security
Understanding Phishing Attacks. Phishing attacks are a prevalent form of cybercrime where attackers attempt to steal sensitive information such as usernames, passwords, and credit card details by... Read More
Protecting Your Data in the Digital Age
Posted on July 22, 2025 Security
Introduction to Data Protection. In the digital age, protecting your personal and professional data has never been more critical. With cyber threats on the rise, understanding how to safeguard... Read More

🔥 Popular Posts
- How to Cook Delicious Meals on a Budget 357 views
- How to Cook Delicious Meals Easily 353 views
- Top 10 Must-Try Recipes for Beginners 352 views
- How to Start a Successful Blog Quickly 351 views
- Easy DIY Home Decor Ideas for Beginners 351 views
- Easy Recipes for Quick Weeknight Dinners 349 views
- 10 Must-Try Recipes for Busy Weeknights 349 views
- 5 Effective Strategies for Weight Loss 340 views
- The Ultimate Guide to Personal Finance 340 views
- Secrets to Mastering Public Speaking Skills 339 views
- Easy DIY Home Decor Ideas for All 335 views
- How to Start a Successful Blog Today 335 views
- How to Start a Successful Blog Fast 334 views
- The Role of Machine Learning in Finance 334 views
- Creative DIY Projects for Home Decor 329 views
- How to Stay Fit Without a Gym 327 views
- Smart Strategies for Investing in Stocks 327 views
- The Complete Beginner's Guide to Yoga 326 views
- The Best Workout Routines for Beginners 324 views
- The Science Behind Better Sleep Habits 321 views